AWS Security
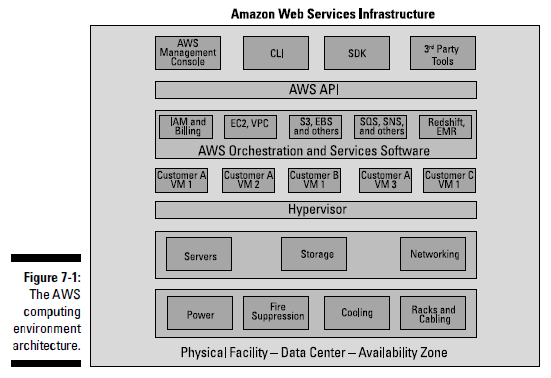
Security is the number-one concern voiced by IT professionals about cloud computing. If you use AWS, you’re likely to improve many elements of your computing security. The provider handles security on one side of the trust boundary, and you’re responsible for the corresponding security on your side of the trust boundary. For Amazon EC2, the location is simple: The trust boundary is located at the hypervisor — the software layer that provides virtualization of AWS instances. Security below the hypervisor is Amazon’s responsibility; everything above the hypervisor is your responsibility.
Security is a shared responsibility, and each party must do its job properly for an application running in a cloud computing environment to be secure. The placement of the trust boundary at the instance means that Amazon takes responsibility for the security of these parts of the computingenvironment:
✓ The physical facility: The data center; its access controls for people;and all power, cooling, and Internet connectivity and networking fromthe building’s perimeter to the rack containing computing equipment
✓ The computing hardware: All servers, storage, and networking devices
✓ The hypervisor: The instance manager and the virtual machines withinwhich instances run
✓ The surrounding software infrastructure: The software that manages all AWS services and provides the automation that allows you to operate your application without ever needing to interact with another human
✓ The Application Programming Interface (API): The true AWS interface,where all outside interaction with AWS is controlled
If you think about it, this concept is fantastic: Amazon takes on a huge amount of the security load that you’re ordinarily responsible for, which reduces the amount of work you have to do — and the investment you need to make.O f course, as noted, security is a shared responsibility, and some security elements remain with you. Here’s a brief list:
✓ Your application’s software packages: They contain all the softwarethat makes up your application, including any software components youwrite.
✓ Your application’s configuration: To maintain an application’s protection, it’s often critical to configure software packages correctly in order to ensure that no malevolent actor can access them and cause havoc.
✓ Your application’s operating system (possibly): This one is a bit tricky —and it relates directly to my earlier characterization of your securityresponsibility as “starting with the hypervisor” as being “a bit glib.”It all depends on who is responsible for the image you use. If you usean image created by someone else (either Amazon or a third party), the security for the operating system and operating system packages resides with the image provider, including not only the general operating system (Windows 2008, for example, or Ubuntu Linux) but also all patches to the operating system, system software (the identity management system, for example), and, possibly, middleware (say, the Tomcat Java application server).
An Amazon Machine Image (AMI), or image for short, is the template from which a running instance (also known as the virtual machine) is launched. The image contains all of the information necessary for AWS to construct a running instance: the operating system, any software components that are contained within the image, and all configuration settings for the operating system and software components that were set at the time of image creation.
The Deperimeterization of Security
When calculating your various security responsibilities, you may have to consider the effects of a concept known as the deperimeterization of security.
✓ Security measures must be present on every computing resource.
✓ These measures must be capable of protecting the resource without depending on external, perimeter-based security services.
By default, any security measures you want to take have to be located within your application and computing resources. The prototypical example of the kinds of protection you can locate within your application and computing resources is IDS/IPS (Intrusion DetectionSoftware/Intrusion Protection Software). Many organizations install IDS/IPS hardware appliances as gatekeepers through which all outside network traffic must pass before being sent on to specific servers or virtual machines.
Amazon doesn’t let you install an IDS/IPS device in its network. The way to address this problem is to install host-based intrusion detection software, or HIDS, on your AWS instances. (The letters IDS also incorporate IPS — even techie types couldn’t stomach a HIDS/HIPS acronym.) HIDS performs exactly the same function as an IDS/IPS appliance, but doesn’t require installing any hardware within the network.